Uncategorized
How do Fake IDs Scan
How Do Fake IDs Scan
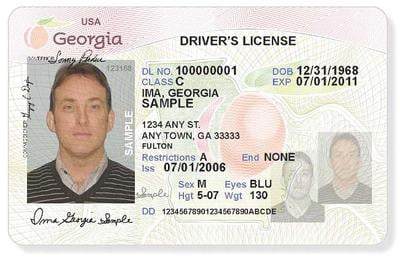
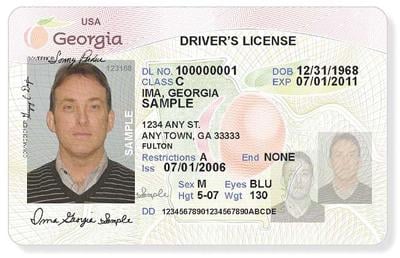
How do Fake IDs scan? This topic is often discussed in relation to modern identification systems, digital security, and automated checks. Rather than focusing on outcomes, this article approaches the subject from a systems and data-flow perspective, explaining how scanners interpret information and why scanning behavior can vary across environments.
The Concept of Data Encoding in Identification
To understand how do Fake IDs scan, it helps to begin with data encoding. Many identification cards—legitimate or not—contain machine‑readable elements such as barcodes or magnetic stripes. These elements are designed to store information in a structured format that machines can interpret.
When a card is scanned, the scanner is not making a judgment. It is simply translating encoded symbols into readable text. This technical process exists independently of who issued the card.
Scanner Design and Purpose
Another way to explain how do Fake IDs scan is by looking at scanner intent. Scanners are built for efficiency and consistency. Their primary goals are:
- Speed of data retrieval
- Accuracy in decoding
- Compatibility with standard formats
Because of this, scanners respond to structure, not authority. If the structure is readable, data may appear on the screen.
Why Scan Results Differ by Location
One reason the question how do Fake IDs scan produces varied answers is that scanners are not all the same. Different environments use different tools:
- Retail systems may focus on age or date fields
- Access systems may only check validity windows
- Administrative systems may apply deeper logic rules
As a result, scan behavior can differ even when the same card is presented.
The Role of Software Rules
Beyond hardware, software plays a major role in how do Fake IDs scan. Many systems apply internal rules after data is read. These rules may evaluate:
- Logical consistency of dates
- Alignment between printed and encoded data
- Pattern compliance with known templates
This explains why scanning is rarely a single yes‑or‑no event.
Why Scanning Is Only One Signal
In discussions about how do Fake IDs scan, it is important to understand that scanning is treated as one signal among many. Modern systems are designed to avoid over‑reliance on a single data point.
This layered approach improves accuracy and reduces errors caused by incomplete or misleading information.
Human Oversight and Policy
Even with automation, human oversight remains central. Professionals trained in verification understand that how do Fake IDs scan is a technical question, not a final decision point. Policies often require staff to combine scanner output with visual review and contextual judgment.
This balance between technology and human input is intentional.
Why the Topic Is Often Misinterpreted
Public discussions about how do Fake IDs scan are sometimes shaped by oversimplified explanations online. Short videos or posts may suggest that scanning is definitive, when in reality it is conditional.
Understanding this nuance helps explain why real‑world systems behave differently than popular portrayals.
Key Takeaways
- Scanning is a process of decoding, not approval
- Structure determines readability
- Software rules shape outcomes
- Human oversight remains essential
Conclusion
So, how do Fake IDs scan when examined from a systems perspective? They interact with scanners the same way any encoded object does: through data structure and format. What happens next depends on software logic, policy rules, and human review.
By viewing how do Fake IDs scan through the lens of technology and system design, the topic becomes clearer, more accurate, and less misunderstood.